31 October 2024
Don’t get phished!
Malicious messages are on the rise. Industry experts estimate that such attacks have risen over 6- to 10-fold since the beginning of the COVID19 pandemic in 2020. In iBizify’s opinion, these threats are now the most significant, beyond traditional malware and direct attacks.
Whilst most attacks are delivered by email, such messages can be delivered via almost any medium including email, text, social media, WhatsApp and even phone calls.

These threats deceive people into revealing sensitive information such as passwords, bank account details, etc. and can be categorised into two variations:
- Phishing: Generalised attacks that are usually sent en masse. The purpose being to catch victims by targeting large numbers within each campaign.
- Spear Phishing: These are highly curated and sophisticated. They usually include more specific information about the targeted individual, such as mentioning several names of people known to the individual, specifying their company name, bank information or specific online services they are known to use.
Seemingly benign phishing attacks are often used to gather intelligence to prepare a Spear Phishing attack.
How do I spot a Phishing email?
THINK BEFORE YOU CLICK! Look out for…
- Urgent, Important, Overdue, flagged as important
- Requests for personal information
- File attachments that lead to very genuine-looking login pages
- Invoices, voicemails or messages waiting for you
- Missed deliveries, parcel tracking
- Your account or password has expired or blocked
- Your computer or account is infected
- Social cues "saw you in this video", "did you really do this?!", etc.
- Claims to be from Apple / Microsoft / Google / Amazon tech support
If you are still convinced the message is genuine, and feel the need to click:
Hover over links to reveal the actual destination. Look at the domain name – the bit before the .com, .co.uk, etc. If the email claims to be from Lloyds Bank, but the destination domain is not a Lloyds domain but rather amazonaws.com (a commonly used tool for phishing) or some other unknown value, then do not click!
Consider not using the email links at all, and instead contact the provider directly using known-good contact information.
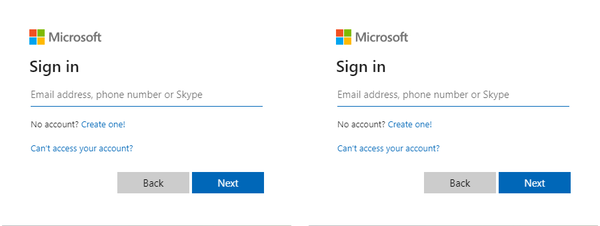
Can you spot the difference between this genuine sign-in page and the fake one?
Be aware
Malicious messages may appear to be from someone you know, they may even include your friend or colleague’s name and contact details. Never assume a message is safe even if it is from a known contact.
You will never get legitimate messages direct from Microsoft / Apple support claiming they have detected malware on your device (or similar).
Never let anyone connect to your device unless you truly know who they are, and have especially good reason to do so.
Be secure
- Maintain your software and devices with the latest updates. Install them promptly and frequently. Don’t forget your PCs, Macs, Android, iPhone, iPads
- USE MULTIFACTOR AUTHENTICATION on any online accounts that you can.
For example, if you use Microsoft online services, set up “Microsoft Authenticator” on your phone. Doing so will help to protect your account even if your password is compromised - ALWAYS use complex passwords for all your online services
- NEVER re-use passwords on multiple online accounts
If you do, if one is compromised, its details will be stored on a database and then used to successfully attack your other accounts (this happens more than you think!) - AVOID using your business email address to sign up for circulars/newsletters or other bulk mail. Doing so shares your email address more widely and makes it harder to filter genuine email. If you want these messages, consider instead setting up a free personal email address to receive them.
- Discuss with your IT provider about how to filter and minimise these attacks
Use password management
Here is an example of a strong password:
8Q{{a>0g13C9gi29.<yW
Could you remember this and type it in every time? Probably not, which is a solid reason to make use of a reputable password manager such as Keeper Security.
Report attacks
For the collective sake of your organisation and others, always report malicious emails if you can. Doing so will help prevent others from receiving the same.
- Check with your organisation’s IT administration or support to see if they have a reporting mechanism.
- Common email tools such as Outlook have dedicated report buttons that you can use. Simply select the message and click the Report Message button.
- If you don’t have these options, consider forwarding the message to report@phishing.gov.uk for the National Cyber Security Centre (NCSC) to review.
Caught out?
If you believe you may have shared your login details or other sensitive information, please change any relevant passwords and contact the host of the service for advice. If you are part of an organisation, then inform your manager. If you shared financial information, contact your bank or card provider as soon as possible. For more information on what to do please visit https://www.ncsc.gov.uk/collection/phishing-scams/what-to-do.
Need help?
If your organisation is an iBizify Manage subscriber, we will already be supporting you in securing your systems and helping your staff to work safely.
iBizify offers a wide range of managed security tools and services from backups, and password managers to vulnerability and endpoint assessments, and online security baselining.
If you have any questions or would like to discuss your IT security, then contact us by scheduling a call at https://ibizify.net/callback/
Blog
- Sophisticated new phishing attacks
- Don’t get phished!
- How to set up Microsoft Authenticator
- Understanding your Microsoft 365 email quarantine
- Development and integration hours - simplified
- We have a new logo
- We have moved
- What to look for in a PC for your small business
- Why you should get to know Microsoft Teams
- Making a splash with Acorn Commercials
- Steve raised over £685 for Marie Curie